Simple Network Management Protocol (SNMP)
What is Simple Network Management Protocol (SNMP)?
Simple Network Management Protocol (SNMP) is an application-layer protocol for monitoring and managing network devices on a local area network (LAN) or wide area network (WAN).
The purpose of SNMP is to provide network devices, such as routers, servers and printers, with a common language for sharing information with a network management system (NMS).
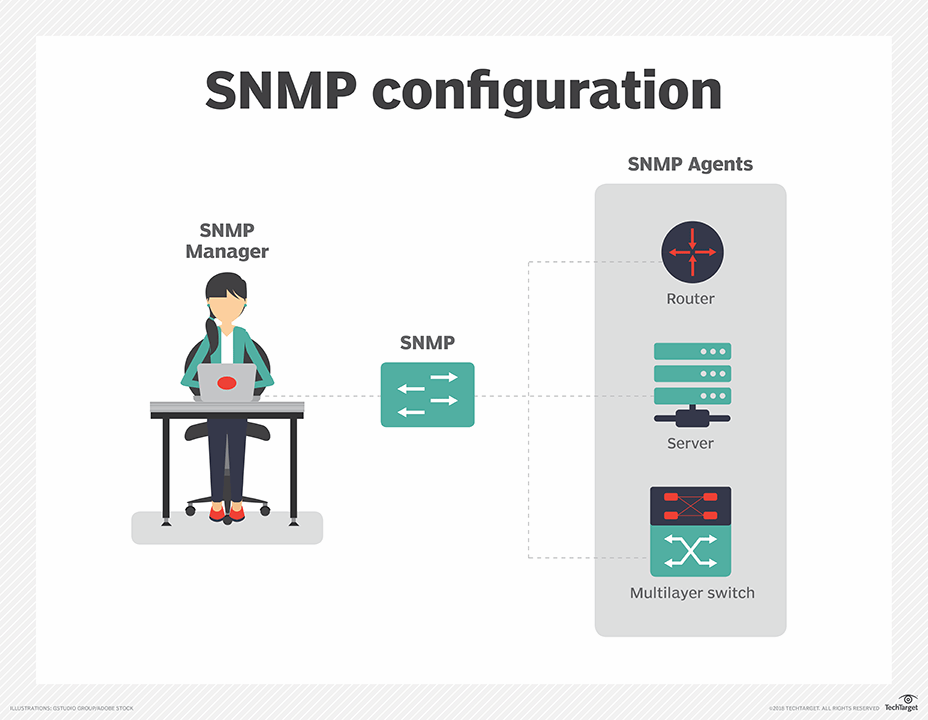
SNMP's client-server architecture has the three following components:
- an SNMP manager;
- an SNMP agent; and
- a management information base (MIB).
The SNMP manager acts as the client, the SNMP agent acts as the server and the MIB acts as the server's database. When the SNMP manager asks the agent a question, the agent uses the MIB to supply the answer.
SNMP is so popular that most network devices come pre-bundled with SNMP agents. To make use of the protocol, however, network administrators must first change the default configuration settings of their network devices so SNMP agents can communicate with the network's management system.
SNMP is part of the original Internet Protocol (IP) suite as defined by the Internet Engineering Task Force (IETF). Multiple versions of the SNMP protocol exist. The most recent version, SNMPv3, includes security mechanisms for authentication, encryption and access control.
How SNMP works
SNMP software agents on network devices and services communicate with a network management system to relay status information and configuration changes. The NMS provides a single interface from which administrators can issue batch commands and receive automatic alerts.
SNMP relies on the concept of an MIB to organize how information about device metrics gets exchanged. The MIB is a formal description of a network device's components and status information.
MIBs can be created for any network device in the Internet of Things (IoT), including IP video cameras, vehicles, industrial equipment and medical equipment. In addition to hardware, SNMP can be used to monitor services such as Dynamic Host Configuration Protocol (DHCP).
SNMP uses a blend of pull and push communications between network devices and the network management system. The SNMP agent, which resides with the MIB on a network device, constantly collects status information but will only push information to the NMS upon request or when some aspect of the network crosses a pre-defined threshold known as a trap. Trap messages are typically sent to the management server when something significant, such as a serious error condition, occurs.
SNMP also includes an inform message type that enables a network monitoring tool to acknowledge messages from a device. Inform messages enable the agent to reset a triggered alert. Network management tools can also use a set message to make changes to a network device through the SNMP agent. This capability enables the network manager to make change device configurations in response to new network events.
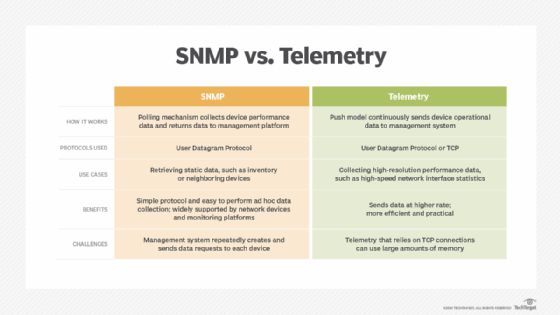
In most cases, SNMP functions in a synchronous model, with communication initiated by the SNMP manager and the agent sending a response. Typically, SNMP uses User Datagram Protocol (UDP) as its transport protocol. Well-known UDP ports for SNMP traffic are 161 (SNMP) and 162 (SNMPTRAP). These two ports are fundamental defaults and are the same in all versions of SNMP.
SNMP is called "simple" because of the uncomplicated nature of the protocol's architecture. SNMP can issue read or write commands, such as resetting a password or changing a configuration setting. It can also report back how much bandwidth, CPU and memory are in use.
One of the most widely used protocols, SNMP is supported on an extensive range of hardware -- from conventional network equipment like routers, switches and wireless access points to endpoints like printers, scanners and IoT devices.
Components of SNMP
There are four main components in an SNMP-managed network.
1. SNMP agent
Agent software runs on the hardware or service being monitored, collecting data about disk space, bandwidth use and other important network performance metrics. When queried by the SNMP manager, the agent sends the requested information back to the management system. An agent may also proactively notify the NMS if an error occurs. Most devices come with an SNMP agent pre-installed but it typically needs to be turned on and configured.
2. SNMP-managed network nodes
These are the network devices and services upon which the agents run.
3. SNMP manager
The NMS is a software platform that functions as a centralized console to which agents feed information. The NMS will actively request agents to send updates at regular intervals. What a network manager can do with that information depends heavily on how feature-rich the NMS is.
There are several free SNMP managers available, but they are typically limited in their capabilities or the number of nodes they can support. At the other end of the spectrum, enterprise-grade platforms offer advanced features for more complex networks, with some products supporting up to tens of thousands of network nodes.
4. Management information base
This MIB database is a text file (.mib) that itemizes and describes all objects on a particular device that can be queried or controlled using SNMP. Each MIB item is assigned an object identifier (OID).
SNMP commands
SNMP can perform a multitude of functions, using a blend of push and pull communications between network devices and the management system. It can issue read or write commands, such as resetting a password or changing a configuration setting. It can also report back how much bandwidth, CPU and memory are in use, with some SNMP managers automatically sending the administrator an email or text message alert if a predefined threshold is exceeded.
Most of the time, SNMP functions in a synchronous model, with communication initiated by the SNMP manager and the agent sending a response. These commands and messages, typically transported over UDP or Transmission Control Protocol/IP (TCP/IP), are known as protocol data units (PDUs).
Below are common SNMP commands:
- GET Request: Generated by the SNMP manager and sent to an agent to obtain the value of a variable, identified by its OID, in an MIB.
- GETBULK Request: Sent by the SNMP manager to the agent to efficiently obtain a potentially large amount of data, especially large tables.
- GETNEXT Request: Sent by the SNMP manager to the agent to retrieve the values of the next OID in the MIB's hierarchy.
- INFORM Request: An asynchronous alert similar to a TRAP but requires confirmation of receipt by the SNMP manager.
- RESPONSE: Sent by the agent to the SNMP manager, issued in reply to a GET Request, GETNEXT Request, GETBULK Request and a SET Request. Contains the values of the requested variables.
- SET Request: Sent by the SNMP manager to the agent to issue configurations or commands.
- TRAP: An asynchronous alert sent by the agent to the SNMP manager to indicate a significant event, such as an error or failure, has occurred.