
jamesteohart - stock.adobe.com
DevOps security pros share steps for success
DevOps security isn't a technical problem -- it's a people and process problem, experts say. Enterprise IT pros offer their advice on how to solve it.
There are plenty of tools for DevOps security -- it's getting teams to use them, and use them effectively, that's the challenge.
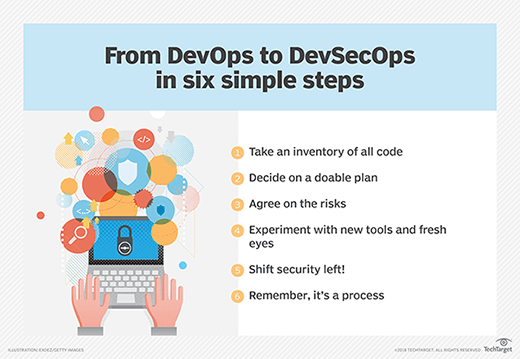
DevOps security, sometimes called DevSecOps, usually includes the concept of "shifting left" -- moving security testing into the early phases of software development, rather than assessing code security just before production deployment. It also usually involves teaching developers to code securely from the start.
Instilling skills and promoting procedures among people isn't as straightforward as installing a piece of software on a machine, but there are still best practices that can help. Above all, patience is required, according to IT pros who have successfully established DevOps security practices at large companies. They spoke in presentations at a GitLab virtual event this week.
"Many days throughout my career, I've felt like I'm, somewhat hopelessly, trying to teach [my] labradoodle to write good software," said Doug Rickert, senior product security manager at Here Technologies, a location services and mapping company based in the Netherlands. "But I still feel like we've made big strides."
More than 600 Here Technologies developers have begun to use GitLab's built-in Static Application Security Testing (SAST) tools over the last year, Rickert said. About 350 have begun to use application dependency scanning in their development process.
Consolidate, automate, templatize
DevOps was a do-it-yourself endeavor in its early days of enterprise adoption, but centralized DevOps platforms are increasingly common as organizations look to hone their efficiency and maintain standards of corporate control over software development.
DevOps security benefits from this trend, in part, because security tools can be built into the interfaces developers already use, GitLab event presenters said.
"Teams moved to GitLab [continuous integration] on their own, especially [since] we had CI templates ready for them to consume," said Sean Corkum, assistant director of engineering at Northwestern Mutual, a financial services company in Milwaukee. "As it stands now, GitLab CI represents 97% of all pipeline jobs here at Northwestern Mutual, which [does] about 45,000 jobs per day."
The freedom to choose development tools is an important part of the DevOps ethos, but some amount of standardization is key to taming the chaos that can come from every team in a large company going its own way, Corkum said.
"It forces developers to learn where all the files are and what's in the pipeline for that team every time they move to a new group," he said. "There's always going to be some give and take, but sometimes operability needs to be prioritized over extensibility."
Improved security is a key part of the operational benefits of a centralized DevOps platform, too, Corkum said.
"Our 'everything as code' mantra has helped us better leverage GitLab through our own tools such as Secrets Detector, which prevents people from committing secrets in their code in the first place," he said. "We've also created other tools to automatically check that you have all the required security scanning jobs in your pipeline, [and] that you're not trying to cheat the system and have jobs set to allow failure."
Measure results
A centralized DevOps platform also lends itself to data analytics to help improve developers' practices, which includes DevOps security, the presenters said.
"Now that everyone's in one [source code management tool], we have a wealth of information ... we can [use] to start working to uplift the entire organization, not just the greenfield projects," Corkum said.
Corkum's team can look at data on merge requests, for example, to double-check whether teams have followed proper security procedures in responding to them.
"We can do targeted messaging to the teams so they know exactly which repos still need to be addressed," he said. "You can ensure teams are using best practices with their repos and pipelines, and those that aren't, you can see who they are and reach out to them and help them along ... [including] making sure teams are using the right scanning tools and using them correctly."
Data-driven analysis has also been important to DevOps security progress at Rickert's company. Analyzing code repositories can help the security team identify common vulnerabilities among development teams and offer training to mitigate them or add automation to make related tasks easier.
"We started looking at concerns in our SAST and secrets detection scan results," he said. "We've been rolling out GitLab's [HashiCorp] Vault integration over the past six months to provide a seamless password experience for our projects."
Sell, don't mandate
Dangling the proverbial carrot is much more important than wielding a stick to promote good DevOps security practices, the presenters said.
"When you're focusing on the mandate, teams don't understand ... the security value you're trying to bring to their product," Rickert said.
It also helps to focus on the convenience of using the 'path of least resistance' in the centralized CI/CD platform, which frees developers from having to customize systems and security tools on their own, he said.
Learning DevOps security can be made even more fun -- a team at Northwestern Mutual used GitLab data to 'gamify' the process of reaching DevOps maturity, Corkum said. Teams can also be rewarded with a prize for being the first to address a merge request, for example.
"This application they created ... was able to help implement better DevOps practices with various tiers, giving teams kudos and perks, including not needing to go to the Change Advisory Board anymore," he said.
GitLab unveils DevOps security roadmap
As IT pros tackle people and process issues, DevOps security tools continue to mature. Here's what's planned for future GitLab releases, according to vendor officials at this week's virtual event:
Expanded code scanning. The next version of GitLab's SAST tool will formalize attack and vulnerability patterns and reuse them across programming languages. GitLab will also offer Dynamic Application Security Testing and container scans on apps running in production to identify stale container images and alert developers to previously undetected vulnerabilities.
Workflow updates. A Workspace UI management tool in development will make it easier to display security monitoring data to users. Other workflow optimizations will include policy enforcement for scanning and security approvals, and remediation time tracking for vulnerabilities.
Known issues. GitLab officials said the company and open source community will have fixes soon for customer feature requests around vulnerability resolution and secrets detection for API keys.
Beth Pariseau, senior news writer at TechTarget, is an award-winning veteran of IT journalism. She can be reached at [email protected] or on Twitter @PariseauTT.






