
DevSecOps
What is DevSecOps?
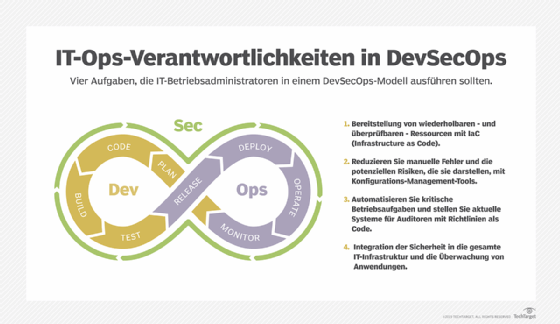
DevSecOps (development plus security plus operations) is an approach that combines application development, security, operations and infrastructure as code (IaC) in an automated continuous integration/continuous delivery (CI/CD) pipeline.
The main objective of DevSecOps is to automate, monitor and apply security at all phases of the software lifecycle: plan, develop, build, test, release, deliver, deploy, operate and monitor. Applying security at every stage of the software development process supports CI/CD, reduces the cost of compliance and enables faster software delivery.
DevSecOps means that every employee and team is responsible for security from the outset, and they must make decisions efficiently and put them into action without forfeiting security.
How DevSecOps works
A typical DevSecOps workflow is as follows:
- Software is developed using a version control system.
- A different team member analyzes the changes made to the application for security weaknesses, overall code quality and possible bugs.
- The application is deployed within security configurations.
- Automation is used to test the application's back end, user interface, integrations and security.
- If the application passes the tests, it is moved to the production environment.
- In the production environment, various monitoring applications and security software monitor the application.
Differences between DevOps and DevSecOps
DevOps is a methodology under which developers and operations teams work together to create a more agile, streamlined software development and deployment framework. DevSecOps aims to automate key security tasks by embedding security controls and processes into the DevOps workflow. DevSecOps extends the DevOps culture of shared responsibility to include security practices.
The DevOps and DevSecOps approaches are similar in some respects, including their use of automation and continuous processes to establish collaborative cycles of development. However, DevOps prioritizes speed of delivery, whereas DevSecOps emphasizes shifting security left, or moving security to the earliest possible point in the development process.
Benefits of DevSecOps
The benefits of adopting DevSecOps include the following:
- improved quality and security of software;
- faster software delivery;
- enhanced communication and collaboration between teams;
- faster recovery from security incidents;
- better cloud service deployments with strong security protocols;
- faster response to ever-changing customer needs;
- earlier identification and correction of vulnerabilities in code;
- increased use of automation, especially in quality control testing; and
- more opportunities for automated builds and quality assurance.
Challenges of DevSecOps
Some of the top challenges of implementing DevSecOps are as follows:
- Teams are reluctant to integrate. The essence of DevSecOps is integrating teams so they can work together rather than independently. However, not everybody is ready to make the switch because they're already accustomed to current development processes.
- Battle of the tools. If development, operations and security teams have been working separately, they have likely been using different metrics and tools. Consequently, they might disagree on where to integrate tools, as it's not easy to bring together tools from various departments and integrate them on one platform. The challenge is selecting the right tools and integrating them properly to build, deploy and test software in a continuous manner.
- Implementing security in CI/CD pipelines. Generally, security has been thought of as something that comes at the end of the development cycle. However, with DevSecOps, security is part of CI/CD. For DevSecOps to succeed, teams can't expect DevOps processes and tools to adapt to old methods of security. By integrating security controls into DevOps workflows, organizations can realize the full potential of CI/CD. When companies deploy security or access control technologies from the beginning, they ensure that those controls are in line with a CI/CD flow.
DevSecOps tools
DevSecOps tools include the following:
- ThreatModeler is an automated threat modeling tool that can be deployed on premises or in a cloud instance. ThreatModeler continuously monitors threat models for cloud computing environments, notifying users of updates and changes. ThreatModeler provides a bidirectional API to integrate with CI/CD tools, enabling teams to build secure cloud infrastructures. ThreatModeler offers reusable templates and built-in threat information and frameworks.
- Acunetix is a web security scanner intended to help developers find vulnerabilities as early in the development cycle as possible. Acunetix enables organizations to protect their web assets from hackers by providing specialized technologies that developers can use to detect and fix issues.
- Checkmarx offers a static application security testing (SAST) tool that scans for security vulnerabilities in code. This tool helps developers deliver secure, reliable applications by incorporating code security analysis and testing into the development process. Checkmarx integrates with a variety of CI/CD tools and environments.
- Aqua Platform from Aqua Security is an application security tool for containers and their infrastructures designed to prevent intrusions and vulnerabilities throughout the DevSecOps pipeline. Aqua implements runtime security processes and controls and focuses on vulnerabilities related to network access and application images. Aqua integrates with a variety of infrastructures, including Kubernetes, to secure clusters at the lowest network level and control container activity in real time using behavior profiles based on machine learning.
DevSecOps skills
DevSecOps engineers need the technical skills of development and IT professionals as well as knowledge of the DevOps methodology. They also need deep knowledge of cybersecurity, including the latest threats and trends.
The following are among the main skills DevSecOps engineers need:
- understanding of the DevOps principles and culture;
- knowledge of programming languages, such as Bash, Go, Python and C;
- strong communication and teamwork skills;
- understanding of risk assessment techniques and threat modeling;
- up-to-date knowledge of cybersecurity threats, software and best practices; and
- understanding of DevOps and DevSecOps tools such as Kubernetes, Ansible, Chef, Puppet and Aqua.
Best practices for supporting a DevSecOps team
The following are three best practices for supporting a DevSecOps team:
- Implement automation to secure the CI/CD environment. One of the key aspects of the CI/CD environment is speed. Automation is necessary to integrate security in this environment, as is embedding the essential security controls and tests across the development lifecycle. It's also important to add automated security testing to CI/CD pipelines to enable real-time vulnerability scanning.
- Address open source security concerns. The use of Open Source tools for application development is increasing. Therefore, organizations need to address the security concerns around the use of such technologies. Because developers are often too busy to review open source code, it's important to implement automated processes to manage open source code as well as other third-party tools and technologies. For example, utilities such as the Open Web Application Security Project's (OWASP) Zed Attack Proxy can check for vulnerabilities in code that depends on open source components.
- Integrate application security systems with task management systems. This will automatically create a list of bug tasks that the information security team can execute. In addition, it will provide actionable details, including the nature of the defect, its severity and the necessary mitigation. As such, the security team can fix issues before they end up in the development and production environments.







